Goregaon (West), Mumbai
Sunday - Friday: 9 am - 8 pm
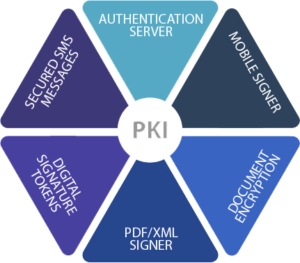
PKI
The purpose of a PKI is to facilitate the secure electronic transfer of information for a range of online activities such as e-commerce, internet banking, online transactions etc. It is required for activities where simple passwords are an inadequate authentication method and more rigorous proof is required to confirm the identity of the parties involved in the communication and to validate the information being transferred.
In cryptography, a PKI is an arrangement that binds public keys with respective user identities by means of a certificate authority (CA). The user identity must be unique within each CA domain. The binding is established through the registration and issuance process. Depending on the assurance level of the binding, this may be carried out by software at a CA or under human supervision. The PKI role that assures this binding is called the registration authority (RA). The RA is responsible for accepting requests for digital certificates and authenticating the person or organization making the request.
A PKI consists of:
- A certificate authority (CA) that both issues and verifies the digital certificates
- A registration authority which verifies the identity of users requesting information from the CA
- A central directory—i.e., a secure location in which to store and index keys
- A certificate management system.
- A certificate policy
Certificate contains amongst other information:
- The CA’s identity
- The owner’s identity
- The owner’s public-key
- The certificate expiry date
- The CA’s signature of that certificate
With strong core competencies in Cryptography and Internetworking, ACE Technology offers solutions built around the Public Key Infrastructure, the framework that provides confidentiality, authentication, privacy, and non-repudiation.
ACE provides range of software applications based on cryptographic algorithms and protocols. Our products are targeted at addressing the internal needs of an organization as well as their interactions with each other, generally leveraging the Internet.
Our offered products have always been on the cutting edge, with a customer focus that has helped us in carrying out quick deployments, minimum customer pain and repeat revenue.

